Spectrum Management Advances in the Queue
Sharing a finite resource requires unprecedented cooperation. 
The rise in the number of technologies that demand their place on the spectrum calls for a balance among the military, federal government and commercial sectors.
Add spectrum management to the list of the
The ascent to prominence has been less a well-paced drive to itemize what needs attention and more the result of a collision between supply and demand. Squeezed between spectrum auctions and the consumer frenzy for innovative wireless products, the U.S. Defense Department is trekking toward standards, acquisition practices, training programs and new tools to deal with the crunch.
Regardless of how the military got into this situation, spectrum management is now a pressing matter. Warfighters today need spectrum not only for radio communications but also for the dozens of new capabilities they have come to rely on such as global positioning systems (GPS), radars and information-gathering sensors.
Mired in the mission to ensure that warfighters have the spectrum they need when they need it are the information technology leaders of both the U.S. Defense Department and the Joint Chiefs of Staff. John Grimes, assistant secretary of defense for networks and information integration and chief information officer, U.S. Defense Department, and Vice Adm. Nancy Brown, USN, director of command, control, communications and computer (C4) systems, J-6, the Joint Staff, are working closely together to address the policy angle of the issue. Collaborating with the combatant commanders, the two are gathering information about procurement, products, processes and problems to coordinate the Defense Department’s solutions to a multifaceted challenge.
This work comes none too soon for warfighters in current missions. Grimes and Adm. Brown relate that early in operations in the
“Understanding that we’ve made that mistake, it’s now a matter of making sure that we think through the spectrum issues, providing enough training so that soldiers are able to use the capability we’re sending over there and ensuring that the capability is not negatively impacting operations, it’s enhancing them,” she says.
Grimes notes that several of the equipment conflicts occurred because some military units were able to purchase upgraded equipment, while others were not. The result was a disconnect between interoperability and spectrum issues. “There was poor planning. Today though, we have fixed that. They have to do an interoperability checklist and testing before the unit deploys to the theater,” he explains.
This problem can be compounded when militaries from other nations are partners in the fight. On the international side of the spectrum issue, two challenges exist. First, countries that are part of a coalition may have devices that conflict with
“This is one of the big topics always at NATO. Under interoperability is the spectrum so that when units of different countries show up for a mission, they are interoperable. The Joint Tactical Radio System is a software-defined radio that is supposed to be the primary answer to that,” Grimes shares.
Adm. Brown and Grimes agree that this means that the
Spectrum challenges are emerging from another area as well. As the demand for wireless devices by consumers has grown and the commercial sector has raced to profit from this demand, the frequency band has become more crowded. “In the past, we operated alone. Nobody else was in our spectrum. It was military spectrum, and that was pretty universal,” Adm. Brown explains. “It hasn’t been until we’ve gotten into the age now of wireless and all of the other capabilities—cell phones and the technology that everybody’s using—that the military spectrum has been encroached upon. So those things weren’t that important before because we weren’t competing for spectrum anywhere. Now, everywhere we go, we’re competing. We compete in the
The solutions to these challenges are multifold. Adm. Brown suggests that the Defense Department urge companies to design new technologies that allow the military to coexist with the commercial sector in the same spectrum. One example would be frequency-hopping systems that employ new techniques that make the finite resource more usable. “We really need to press the commercial folks to come up with new ways to make our use of spectrum much more efficient. To be quite honest, we didn’t pay much attention to spectrum until recently. It’s really on us to do a much better job when we buy equipment to look at spectrum up front and not wait until the very last minute to say, ‘Oh, we don’t own that spectrum. You can’t operate that technology in that spectrum for us,’” she relates. To this end, spectrum supportability assessments are being conducted much earlier in the acquisition process than before, the admiral adds.
Systems developers can help solve spectrum issues in other ways, including spectrum management. Grimes points out that the military has been working with its research and development arm, the Defense Advanced Research Projects Agency, as well as the Defense Information Systems Agency to improve future systems and to resolve problems with current systems.
Two spectrum management tools already are in the pipeline for military use. The Global Electromagnetic Spectrum Information System (GEMSIS) is the program of record that allocates spectrum in the manner similar to how air tasking orders are issued to send aircraft on missions. It will enable the services to coordinate spectrum from a joint perspective based on information about which spectrum is required and how various devices radiate. This will allow the military to put a spectrum plan together for an operation to an extent that has not been possible before, the admiral says. The introduction of GEMSIS into the field is expected in 2008.
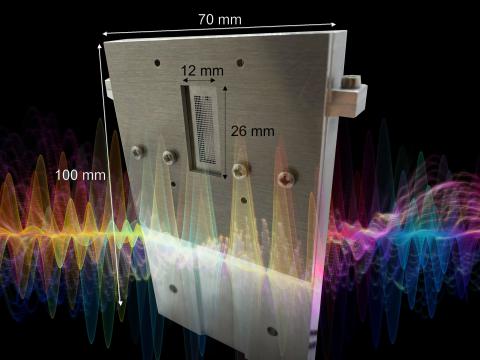
The Coalition Joint Spectrum Management Planning Tool (CJSMPT), which is still in the joint capabilities technology demonstration phase, is the second system that will help the services better manage spectrum use. This automated tool interfaces with all of the various spectrum databases in the services and ties all the service-unique databases together so a spectrum manager understands what is available. “It also allows them to go in and figure out what spectrum different devices use, so it provides the information they need to develop a spectrum plan for the operation,” Adm. Brown explains. As envisioned, the CJSMPT will feed into GEMSIS and facilitate the creation of spectrum tasking orders.
The department sent the CJSMPT to
“We don’t expect to take the CJSMPT back from the soldiers in
As new spectrum management technologies roll into the field, the importance of training skyrockets. Training is an area that has been largely ignored recently, the admiral admits, but that situation already is changing. After eliminating spectrum specialist as a career field a few years ago, the U.S. Army is bringing it back. A C4 Planners course, which features a segment on spectrum, will begin next month. One of Adm. Brown’s priorities is to elevate the importance of the spectrum management profession, including developing a core group of experts who can continue to manage the spectrum for the military. “This is one of those skills that we just haven’t emphasized enough,” she says.
Grimes notes that the Defense Department did not envision the demand for spectrum and spectrum management at the beginning of the Global War on Terrorism. Each service had its own training program, and the complexity of spectrum interference and operational problems in the theater required the Army to “borrow” about 250 Navy-trained electronic warfare officers who were assigned to the Army units. “Now, the Army has established a school at
Adm. Brown and Grimes agree that resolving spectrum issues is going to require cooperation on a grand scale. Companies must create products that are spectrum efficient. The military must test equipment for use in the
This last issue is one that Adm. Brown is cautiously optimistic about. “I think what’s different today is that we’re not arguing about it. We’re trying to figure out together the best solution for all of us. How can we peacefully coexist with this finite resource? Of course we all have different demands and different priorities, but we have to come together and solve it as a team. We can’t fight each other,” she states.
Grimes agrees and points out that it is important to address this problem now because technology development is exploding at a rate that cannot be predicted. “When I was at the White House in the late 1980s and early 1990s, we had this thing just starting called the Internet, and we were looking at some security of our own. Three years later, there was a total explosion. We never envisioned the Internet to take off like that. It’s the same way with WiMAX or any of the other new devices. In fact, we don’t know who’s going to have the next frequency-demanding device that has to operate in spectrum,” he states.
Web Resources
Assistant Secretary of Defense for Networks and Information Integration: www.defenselink.mil/cio-nii
Command, Control, Communications and Computer (C4) Systems, J-6, Joint Staff: www.jcs.mil/j6/index.html