Maryland ‘Guards’ Against Cyber Attacks With Collaboration
With cyber attacks becoming increasingly common, dangerous and complex, state military officials are attempting to get out ahead of the enemy and be proactive rather than reactive.
Maryland cyber crews in the Army and Air Force National Guards acknowledge that to accomplish this effort, they need to build better relationships and communication pathways with each other, private-sector individuals and utility company workers. Through participating in several exercises and tabletop workshops focusing on the cyber arena, defense officials are learning this lesson while creating and fostering connections among these groups and organizations.
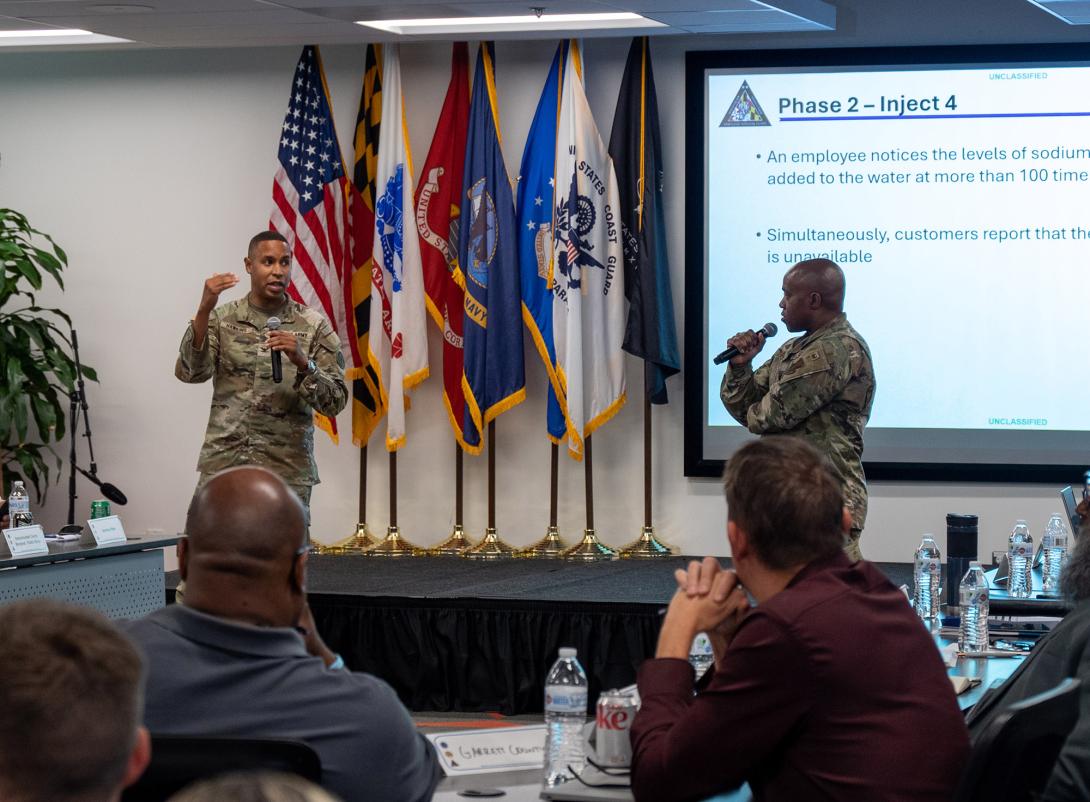
Armed forces personnel are fresh off partaking in a workshop that took place last month: the second iteration of the Critical Infrastructure Cyber Resilience Workshop. This event mirrored the first edition of this series of exercises that occurred in August, but the most recent one focused on energy, while the original focused on water and wastewater, according to Capt. Marissa Robbins, commander of the 169th Cyber Protection Team in the Maryland Army National Guard, and Maj. Benjamin Hughes, public affairs officer in the Maryland National Guard. At the exercise officials held in March, government individuals and leaders in the energy field came together to ponder and deliberate on potential problems in cyberspace to address them before they happen. Rather than approaching Maryland cyber teams after an issue emerges and requesting that they remedy it, they anticipate that by taking part in events like this, they can prevent the problem altogether.
This principle is one that defense cyber teams observed during the original August workshop and one they are looking to further.
“The key takeaway from that event was simply the interaction with those utility partners,” Robbins said during an interview with SIGNAL Media. “I think, overall, we don’t want to meet them for the first time when something goes horribly wrong. We want to already have those connections established, so it really got after that for us, down to the very lower levels to even my team. If something were to happen and operators were sent that way, we [want to] already know them and we [want to] already have a connection.”
The first version of the exercise zeroed in on the water sector of critical infrastructure. Members of the Maryland National Guard hosted the event in conjunction with not only leaders in the water and wastewater industry but also with Department of War (DOW) officials—marking the first time the DOW directly teamed up with a state National Guard for this type of workshop, per Hughes. The gathering provided an opportunity for the parties involved to advance cyber resiliency of the water and wastewater component of critical infrastructure, bolster relationships, exchange lessons learned and establish next steps that adhere to the State-Federal Unity of Effort on Cybersecurity, Hughes added.
Additionally, airmen in the Maryland Air National Guard sought to do their part to advance the cyber field. Members of the Maryland Air National Guard’s 175th Cyberspace Operations Group engaged in its annual capture-the-flag competition late last year, where they had the chance to develop and enhance their offensive and defensive cybersecurity skills. They, along with soldiers in the Maryland Army National Guard Cyber Protection Team, were divided into teams and assigned to find strings of code, hidden passwords, web applications or documents on a simulated network environment. These “flags” provided clues that led participants to their next tasks, according to Air Force officials. The more weaknesses they exposed, the more networks they examined, and the more puzzles they unraveled, the more points they earned for their teams.
The capture-the-flag event was intended for individuals of all skill levels in cyberspace, from beginner to veteran operators. In addition to the training talents that airmen could develop from this exercise, they were also able to analyze and delve deeper into the nature of cyber operations, per Air Force officials.
Furthermore, events like the cyber workshops and the capture-the-flag exercise allow essential personnel in these relevant areas to come together, network and forge partnerships, which is critical for cyber teams to achieve their goal of becoming and staying proactive rather than reactive.
Col. Roger Koehler, commander of the 175th, said there is a fine line between critical infrastructure and defense critical infrastructure. “For the military piece, for our federal missions and for our state missions, it is having those conversations and being prepared so that if there is ever a point where we’re called upon, we’re ready for those types of missions. So, from a force provider, I think it’s really important for us to work together on those things.”
These exercises also give the cyber warfighters the opportunity to create open lines of communication and more effectively get on the same page. “We all have our own lexicon,” Koehler added. “Just between the Army and the Air Force, we have different lexicons a lot of times when it comes to cyber. Then, you start working with state organizations, and they have different lexicons. You start working with industry, and they have different lexicons. And I think getting around the table and kind of talking through [this], you realize a lot of the times that people have different ideas in their mind of the problem they’re going after, and really laying all that out helps improve what you’re trying to accomplish.”

Lastly, military leaders can take advantage of these events to conduct real-world simulations in which they experiment with new tactics, techniques and procedures. Some ideas and proposals are more effective on paper than in reality, so these opportunities allow for the necessary, realistic testing.
“It’s great that these exercises are taking place [and] bringing everybody to the table,” Lt. Col. Cris Horton, task force leader and senior liaison officer in the Maryland Cyber Security Task Force in the Maryland Army National Guard, said. “You can plan for everything you want, but as soon as something happens, it seems like the plans go out the window. [These exercises provide] a great environment that people can come and do ‘if this, then that’ kind of situations around the table here for these exercises, and really work through it on how they respond.”
“Because you can write anything you want to down on a piece of paper, but then you step in and go around a tabletop [exercise]; whether it’s digital or just a tabletop exercise of people putting pieces of paper down with events happening, it takes on a totally different mindset there, and that’s always the way it is with wargaming and [the] military,” Horton added.
Military officials are advocating for a more prepared and dedicated approach to the cyber field not only by hosting and participating in events like these but also by rearranging their force.
The Maryland Air National Guard is now the only state without an Air National Guard flying mission, per Hughes. In September 2025, leaders began the process of converting this group into a cyber wing, giving cyber operators more resources as the mission within this specific space grows. The estimated timeline and completion of this conversion process are up in the air due to logistical unknowns, according to Hughes.
“It’s kind of going to be a little bit of a long evolution,” Hughes said. “Just because the schoolhouse training pipeline takes a while for folks to get through. We’re [also] trying to find jobs and positions for all the folks that were doing flightline and maintenance operations and seeing how many people want to stay in cyber versus convert to other places that they want to or keep doing a flying mission and go to other states and whatnot.”




Comments