NSA Texas Is Open for Cyber Business
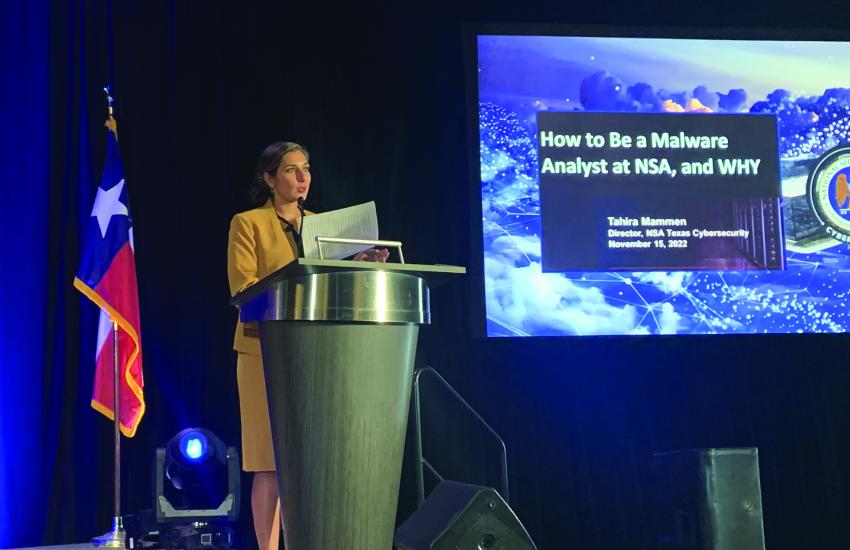
The 3-year-old Cybersecurity Directorate (CSD) at the 70-year-old National Security Agency/Central Security Service (NSA) is growing, especially in Texas. While the agency’s headquarters is at Ft. Meade, Maryland, NSA Texas in San Antonio now hosts about 3,000 employees, reports Tahira Mammen, director, Cybersecurity, NSA Texas. “We have a sizable team here at NSA Texas,” she said, speaking at the AFCEA Alamo ACE event in November.
The agency is expanding its cybersecurity and cryptographic workforce, given the increasing cyber threats facing the United States. The agency works to protect national security-related systems, critical infrastructure and assets related to the defense industrial base, and provides crucial cryptographic tools, Mammen noted.
“There’s two sides to our mission: to prevent and eradicate,” the director explained. “And in that prevent space, we are leaders in NSA’s keys and codes mission. A foundational element of CSD’s posture is to integrate NSA into the design and build of Department of Defense national security weapon systems and their cryptography to ensure that the systems our warfighters are using are resilient to cyber attacks and protect U.S. strategic advantage in times of conflict. CSD performs on a no-fail mission to deliver over 1 million keys to our customers. We enable nuclear command and control, and we analyze and share foreign cybersecurity intelligence.”
The San Antonio region itself has become a cyber center. The military’s Joint Base San Antonio (JBSA), JBSA Lackland and JBSA Randolph are located in the area. The Air Force’s Information Warfare Numbered Air Force that specializes in offensive and defensive cyber operations, the 16th Air Force, is located at JBSA. Port San Antonio, a 1,900-acre industrial area that once was Kelly Air Force Base, is now a cyber and innovation center. And according to the city’s mayor, Ron Nirenberg, San Antonio holds the largest contingent of cyber assets in the United States, outside of the Washington, D.C. region, leading many to dub it Cyber City, U.S.A. The NSA’s CSD presence only adds to the numbers, according to Mammen.
“At NSA Texas we are one of the largest employers in San Antonio,” she stated. “And we are growing…. But I go to a lot of places where people don’t know that you don’t have to live in Maryland or D.C. to support your country at the NSA. We have opportunities around the nation, really, but we’re recruiting heavily right now in Texas.”
The threat picture in the cyber world is only growing in complexity and in the number and frequency of attacks, Mammen continued. “As you know, cyber is a gray space,” she stated. “It is always combative. There’s always an emerging threat from our adversary. And in that gray space, our job at the cybersecurity mission is to provide threat intelligence, mitigations, network security and guidance.”
The directorate succeeded early in finding, understanding and then releasing a list of the most common software, hardware and network vulnerabilities leveraged by the People’s Republic of China (PRC) to attack U.S. systems, steal intellectual property and access sensitive networks. The public-release reporting, which is conducted jointly with the Cybersecurity and Infrastructure Security Agency (CISA) and the FBI, began two years ago and is called, The Top Common Vulnerabilities and Exposures (CVEs) Actively Exploited by PRC State-Sponsored Cyber Actors.
“One of our first big successes in this arena happened in 2020, right after we stood up the Cyber Security Directorate when we released the 25 vulnerabilities that the People’s Republic of China state-sponsored malicious actors were frequently exploiting to target U.S. and allied members,” the director said. “I want you to understand that these were vulnerabilities that as a cybersecurity community we already knew about but [saw how] patching and mitigations were lacking enough across our collective cyber defenses. This [reporting] in 2020 really set the pace for how NSA Cyber was going to partner in the future to prevent exploitation from Chinese state-sponsored hacking.”
Since then, the organizations have updated the report on the PRC-used CVEs three times. “We’ve expanded the methods in which we communicate, and we are not only providing extensive lists of CVEs, but the tactics, techniques and procedures used, and we’re mapping everything to what you need to implement to stop it,” she clarified.
The FBI, CISA and NSA will continue to partner “to stay on top of this mission and to publicly release any active hacking campaigns that are targeting the United States,” Mammen added. “We are constantly updating what people need to be looking out for and patching. These are things we’re putting out with solutions so that you are not a victim of targeted attacks.” This partnership between the federal agencies allows the United States to have “a more comprehensive threat understanding, with comprehensive actions with one coordinated voice,” which is necessary given the constant and rising threats from China.
“The PRC is playing the long game. They are pacing [the] threat; they have become more brazen, economically, diplomatically, militarily and technologically,” Mammen warned. “They have and continue to steal staggering amounts of valuable intellectual property to build their own national infrastructure, with really global ambitions.”
Adversaries are also conducting disinformation campaigns in response to the United States’ disclosure of their attack vectors to try and discredit the CVE information. “In response, we’ve seen nation-state cyber competitors participate in ‘tit-for-tat’ type media campaigns, exposing tools that they alleged to be used by NSA and the CIA,” the director clarified. “They continue to conduct multiple interviews, attempting to disclose information that is honestly a decade old.”
A good portion of malicious cyber activity over the last year has come in the form of ransomware, which CSD has engaged in confronting. “Ransomware is a national security threat,” the director stated. “And the NSA obviously has a role to play in combating it in partnership with the U.S. Cyber Command. Specifically, we focus on ransomware that is targeting the most critical infrastructure and national security systems from the defense industrial base. We’ve joined with U.S. government and private sector partners in working to make ransomware operations more difficult for adversaries. We want these things to be less scalable and, frankly, less lucrative for malicious cyber actors. Our foreign intelligence informs policymakers and diplomats as to how they can pursue the safe havens from which ransomware actors are conducting their attacks.”
In addition, the agency released previously classified reverse engineering software into the public domain in 2019, a key step in fighting attacks. The open-source tool, called Ghidra, helps to speed up the process of identifying and understanding cyber attacks through reverse engineering. The NSA specifies that Ghidra also features a processor modeling language known as Sleigh that interprets how machine language instructions are dissembled and transformed into the tool’s so-called P-code representation. “Other significant functions are an undo/redo feature, multiuser collaboration repository and scripting,” according to NSA Public Affairs Officers Natalie Pittore and Liam Davitt.
“Ghidra, if you’re not familiar, is NSA’s open-source reverse engineering tool that we released three years ago at the RSA Conference,” Mammen explained. “If you’re not familiar with it, it is available to anyone. All of you, even people in college, people in high school. You can download it and have access to really a cutting-edge server security tool of reverse engineering. With the release of Ghidra, we set to build a community of dedicated and educated users. And by making the software free, even students can develop the technical proficiency to work on advanced cybersecurity problems.”
At the same time, the NSA is increasing its capabilities at Ft. Meade. In October, the agency opened a new center as part of its $4.6 billion East Campus expansion of seven buildings—and four parking garages for employees—that began in 2014 and will conclude in 2028. The Morrison Center—named for Maj. Gen. John E. Morrison, USAF, who served as head of the NSA’s signals intelligence organizations in the late 1960s and was the founder of the agency’s National Security Operations Center—will host the NSA’s new National Security Operations Center facilities.
“As digital threats to our nation and allies continue to rise, the Morrison Center is designed to enhance NSA’s ability to defend national security information systems and protect our nation’s critical data,” the agency stated in a release.
In unveiling the facility to reporters in October, NSA Director and Commander of U.S. Cyber Command Gen. Paul Nakasone, USA, noted that the Morrison Center would be a central place for conducting cyber, cryptographic and other operations.
“Why is this place important? Because it’s going to house our nerve center, which is our National Security Operations Center,” he said. “And it is a reflection of the world in which we operate today, which is video, which is at high bandwidth, which is increasingly with the private sector, which is increasingly with a variety of partners. Those are all things that the technology that this center will allow us to do.”
The agency expects the Morrison Center to reach full operating capability in the next six months. “The last major construction, really, was 25 years ago here,” Gen. Nakasone noted. “So, we are anxious to continue to open up our buildings here on the East Campus. I think that what we will find is just a continued greeting of our workforce as they see this and say, “Wow, I really want to work here.”
The kind of people that the NSA needs for cyber and other operations are those committed to defending the nation, Mammen stated. “And if you join us, you’ll get to see these threats from a whole different vantage point.”
She encouraged people of all levels, from high school to college students, veterans, NSA alumni and industry experts, to join the NSA’s cyber mission and project against the PRC and other countries and organizations threatening our security and daily life.
“This is why NSA wants you to be part of our world-renowned globally significant cybersecurity team that uncovers defenses and can see the intricate techniques of our highly capable cyber adversaries,” Mammen stated.



Comments