The Quantum Cryptography Conundrum
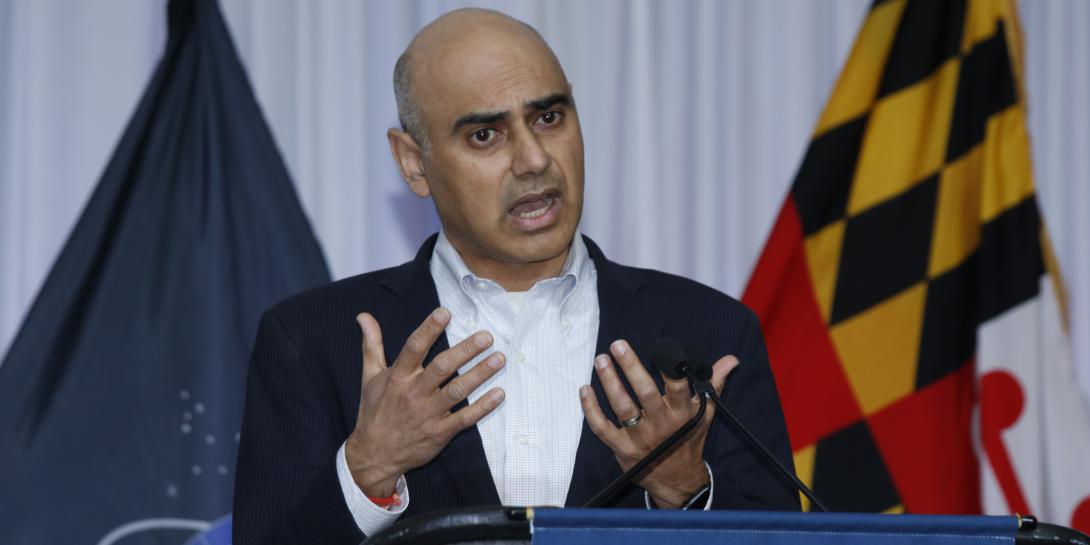
The United States is developing new algorithms to protect against the adversary’s future—powerful quantum computing that will be able to break into currently encrypted systems and data. Led by the National Institute of Standards and Technology, or NIST, seven advanced algorithms are being considered for use as standardized methods. The Defense Information Systems Agency, or DISA, is working with NIST and Defense Department leaders to implement the quantum-resistant cryptography solutions, when ready, into military use, said Deepak Seth, DISA’s chief engineer, Emerging Technologies Directorate.
The chief engineer spoke on April 27 at AFCEA’s TechNet Cyber conference in Baltimore, being held April 26-28.
“Quantum computers offer great promise,” Seth acknowledged. “We hear about them all the time. They promise to really revolutionize computing. They offer breakthroughs in science and engineering. But while it’s an exciting new technology, it also poses a serious security threat. When these computers become operational, our current asymmetric encryption technology today will be rendered insecure.”
Presently, for authentication means, digitally signing documents, sending encrypted messages or encrypting data, the DoD uses asymmetric encryption, Seth explained. “Asymmetric encryption is really the foundation element of our public key cryptography,” he said.
The problem is that these current security mechanisms will not be effective in protecting data from quantum-based attacks, whenever they are operational, whether that is in five, 10 or 15 years. And adversaries could already be taking hold of encrypted information to be broken into later.
“We presume that our adversaries are executing these so-called ‘store now and decrypt later’ attacks, in which they are basically harvesting our encrypted data that flows across the networks and across the Internet,” Seth emphasized. “Adversaries are harvesting it. They are storing it and hoping that when they get their hands on a quantum computer in the future that they’ll be able to decrypt the data and then be able to see what current messages were.”
No one really know when a fully functional quantum computer will be built. It could be 5/10 years. Adversaries do 'store now & decrypt later' by harvesting encrypted data & hoping that in the future that they will be able to see classified info, says Deepak Seth #AFCEACyber pic.twitter.com/c6xBtouiRF
— Kimberly Underwood (@Kunderwood_SGNL) April 27, 2022
Even the well-known Shor’s algorithms will be able to be broken by quantum computers. “If a Shor’s algorithm were to run today on a quantum computer, the time it would take to decrypt the data would be shortened from years to days and even possibly less,” Seth warned. “It is for this reason and many others that DISA is extremely concerned about the threat posed by quantum computing.”
NIST has already identified seven possible quantum resistant algorithms that could be used to protect against quantum computer-based attacks. Of those seven solutions that appear to have the most promise, the agency will select a final algorithm to be considered for standardization—following the end of NIST’s third round of competition.
“Once these new algorithms are announced and when they are standardized, DISA intends to adopt these NIST standardized, quantum-resistant algorithms for our public key infrastructure,” Seth explained.
Time is of the essence, the chief engineer stressed. DISA and officials across the DoD must start to examine now how they will integrate the quantum-resistant algorithms into their existing networks and operations.
“We have to prepare ourselves now for integration to be able to use these new encryption algorithms,” Seth said. “It has taken us years to field new security solutions into DoD networks and IT systems and to make things worse, these new NIST quantum-resistant algorithms will not be as simple as ‘swap out, swap in’ or a drop-in replacement.”
Moreover, the new algorithms won’t be a static solution. “It’s also expected that some of these algorithms will change overtime,” Seth realized. “There will be new variants to these algorithms and some modifications, so we also will need the ability to quickly upgrade new cryptography into our IT infrastructure.”
In addition, the chief engineer advised that organizations start considering post-quantum algorithms and the associated need for updates to infrastructure as part of a modern development security operations, or DevSecOps, software development process.
“It’s a really serious problem,” he stressed. “We have to prepare now to begin to adopt quantum-resistant algorithms and we must do so at the earliest possible time to protect our data from quantum attacks.”


Comments