Meeting Software Shields Data
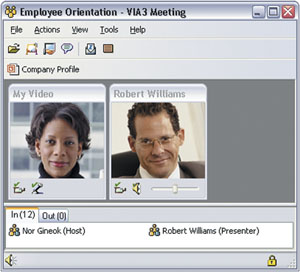 |
| The VIA3 E-Meeting Service allows individuals to meet quickly and securely regardless of their geographic locations. Using advanced encryption architecture, data can be sent across the Internet without being intercepted. Through the program’s suite of office applications such as Microsoft Word, users can collaboratively share, edit and produce documents and presentations. |
The U.S. Department of Energy (DOE) has been using the meeting tool for about a year. According to
Noting that his responsibilities include managing the DOE’s secure conferencing applications, Way says that the meeting tool complements existing capabilities and is not an alternative or replacement. Developed by Viack Corporation,
Because the software uses common applications such as the Microsoft family of office products, users quickly become accustomed to the interface and the collaborative environment it fosters. “In essence, it’s a Microsoft replication. You do everything in the way that you are used to in a Word, PowerPoint or Excel document,” he says.
VIA3 also economizes bandwidth use. With its live video feature activated, it uses 256 kilobytes of bandwidth. Way offers that this scalability makes it more flexible than other applications such as Microsoft NetMeeting, which uses 64 kilobytes on a dial-up connection but immediately jumps to 384 kilobytes on a broadband system or local area network without many options to decrease bandwidth usage.
The service can operate in limited bandwidth environments for dial-up or wireless applications. Way notes that a remote user on a laptop can still access a meeting. Even if the connection cannot provide 64 kilobytes, communication can proceed without video. “It doesn’t matter where you are. If you have Internet access, you’re on,” he says.
The DOE currently is deploying VIA3 to approximately 60 users on a limited basis, and Way believes that in the upcoming fiscal year, other branches of the agency will acquire the software. Because different parts of the organization will use the software independently, he estimates the total pool of potential DOE users to be roughly 400 to 500 individuals.
The Chief Information Office has funded a 12-user license, but each license can accommodate up to four additional meeting participants, allowing a total of 48 users to meet, Way says. He adds that an individual meeting session can accommodate up to 30 participants, depending on network capabilities and video use. Four other DOE program offices also are establishing their own Viack accounts.
The latest version of the software combines audio, video, instant messaging and several standard office software products into a real-time meeting tool. The product uses the advanced encryption standard and has recently received a Federal Information Processing Standards 140-2 level-1 security certification from the Defense Information Systems Agency’s Joint Interoperability Test Command, says Ronald I. Koenig, Viack’s chairman, president and chief executive officer.
VIA3 features information-sharing tools that allow it to be used in many situations. One important function is a real-time video application called Live View, which permits users to share imagery. For example, an analyst could share satellite photographs or other graphic data with a supervisor or with other analysts.
The service includes a suite of Microsoft office products such as Word, Excel and PowerPoint. Participants can display PowerPoint presentations or work collaboratively on a document, making additions, deletions or corrections. This work can be done in a synchronous or asynchronous mode. The system tracks the changes and stores them in a merged file for final approval.
An embedded echo cancellation system permits individuals to use their desktop or laptop microphone and speakers without headphones or other external devices. The echo cancellation system includes an automatic gain control that adjusts the participant’s volume settings. Koenig notes that the audio system operates in a very small footprint that uses only 13 kilobytes of bandwidth to provide full duplex audio.
Although VIA3 can provide video images of session participants, the company has installed governors on this capability. Koenig explains that while Viack could provide high video frame rates, the feature continues to be an extremely expensive use of bandwidth. “For most people, it’s enough to have up to 15 frames per second and to see the image of the person they’re talking to. In fact, it doesn’t have to take up the entire screen,” he says.
Koenig adds that the software is designed to minimize bandwidth use wherever possible. For example, if a user expands a document to full screen size obscuring the video boxes, the program will shut off the video feature until it is needed. Although multiple video images are limited by only the available bandwidth at a specific location, most meetings are typically centered on documents or presentations, he says.
VIA3’s security structure can be tailored for specific users and clearance levels. For example, two users can employ the system’s instant messaging feature to communicate about a document. A limited number of people can then be granted read-only access to the file. A variety of time limits and access systems can be included to audit use, for example, to alert the original sender when a recipient tries to print or electronically copy a document.
The program originally had to be modified to operate more efficiently with firewall software because of security issues involved in adapting firewall ports to accept video and audio input. Koenig notes that even in highly secure environments such as the U.S. Treasury Department’s network, which uses multiple nested firewalls, the software will operate as long as Viack can establish operating protocols with system administrators.
The first versions of the VIA3 service appeared in late 2002. At the time, a specific business plan had not been created to market the product to the government; however, the demand for secure communication systems following the September 11, 2001, terrorist attacks drove sales. The company’s first customers were the DOE and the Treasury Department. Work is underway with several other agencies to develop and evolve the software, Koenig says.
VIA3 was originally designed to provide a secure communications capability. As part of this philosophy, Viack does not have the right to access customer data. All messages are encrypted from the user’s desktop and stored in the company’s servers. “We never keep or have knowledge of passwords,” Koenig explains.
Customers can either store their data in the company’s or their own servers. Because the encrypted data travels over the public Internet, it bypasses the limitations of many enterprise architectures. For example, a Federal Bureau of Investigation (FBI) agent is protected by his or her agency’s network and enterprise facilities when he or she is working from the home office. When he or she is operating from a remote location and communicates with other agents via a hotel room Internet port or a wireless laptop, the information is safe because it is encrypted and decrypted at both ends of the communication. This configuration eliminates the need for the normal network security requirements because the messages do not interact with the architecture. “It takes all network anomalies, network failures and weaknesses out of the equation,” Koenig maintains.
Web Resources
Viack Corporation: www.viack.com
Telework Consortium: www.teleworkconsortium.org



Comments