Army on the Cusp of BYOD Era
Thanks in part to the implementation of zero-trust devices, the U.S. Army is poised to begin a pilot effort allowing U.S. Army Reserve and National Guard personnel to connect their individual communications devices to the service’s network.
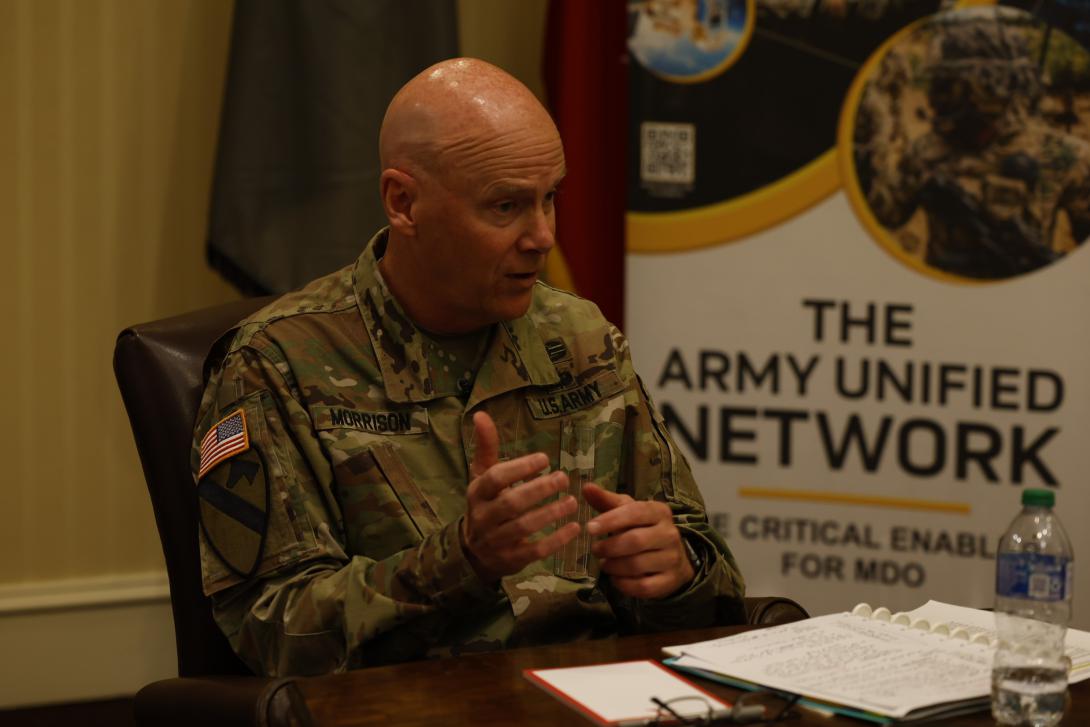
“Bring your own device,” or BYOD, has been a concept for the Army and others in the U.S. military for years, but it proved an elusive goal primarily for cybersecurity reasons. Now, however, that goal is in reach, according to Lt. Gen. John Morrison Jr., Army deputy chief of staff, G-6.
“It has taken us a while to get to this point, both from a policy perspective and from building out the environment, but we are right on the cusp of implementation,” Gen. Morrison told reporters during an August 18th media roundtable discussion at AFCEA’s TechNet Augusta conference in Augusta, Georgia. “What that means is, you can now—much like you do in the commercial sector—use your personal device, but we will put a secure capability on it that allows you to log back into the Army network and conduct official business.”
The pilot effort is set to begin in the September-October timeframe and in time will expand to active-duty components within the continental United States and overseas, he explained. “It’s going to be a fairly broad pilot that we’re looking to do. We’ll work through the physics of how many users it’s going to be. We have the ability to go up to several thousand.”
He stressed that the cybersecurity capabilities that will allow the nonmilitary devices to join the network have been thoroughly tested. “What is very, very important is that we have done cybersecurity assessments all the way along this journey because if you don’t bake in cybersecurity at the very, very front end and do it continuously, then we obviously open up some holes in our swing. That’s been one of the big concerns about anybody using their personal device to conduct business,” he reported.
Lt. Gen. John Morrison, Jr., Army deputy chief of staff, G6, on "bring your own device" pilot program: It has taken us a while to get to this point, both from a policy perspective and from building out the environment, but we are right on the cusp of implementation.#AFCEATechNet
— George Seffers (pronounced See furs) (@gseffers) August 18, 2022
Cloud computing also helps enable the pilot. “Since it’s done in a virtualized environment that is hosted up in the cloud through the [Defense Department], it is very, very, very secure. We have had it red teamed ad nauseam by elements outside of the Department of the Army, and the assessment that came back in said the path that we’re on is one of the most mature that’s out there.”
The bring-your-own-device era will bring multiple benefits for the Army, the general indicated. “Think of the operational effectiveness that will come with that. We have layered in the security, all based off of zero-trust principles, and that notion of knowing who that individual user is. And think of the possible fiscal efficiencies that we potentially get,” he said.
The pilot effort will include both technical experts and average users working together. “The reason we do that is that the technical folks talking to users in that environment, produces—we learned it with Army 365—just amazing TTPs, tactics, techniques and procedures,” Gen. Morrison added.
The bring-your-own-device project will be accompanied by another pilot program focused on virtualization, which is expected to begin about the same time and to also focus initially on the Guard and Reserves.
“We’re doing the same thing with, as I refer to it, our virtual desktop. That’s being run by our enterprise cloud management activity, and we’re actually, from the G-6 perspective, getting the operational components of that moving. Just think of the power of it where you don’t have to buy a laptop everywhere you go to put on a desk. You’re now able to buy a relatively dumb device that when you log into this environment, it’s almost as if you have your own personal desktop,” he offered.
Virtualization offers greater mobility while also enhancing the user experience at remote stations or installations, such as some armories or Reserve centers that do not benefit from a robust military infrastructure. “We are targeting Reserve centers that may be out in remote areas where we may not want to extend military infrastructure, communications. And we can now leverage what is out there with this virtual infrastructure. It will be just like they were at Fort Bragg or Fort Gordon, or you pick a post,” he said.
Both pilots offer similar benefits and both benefit from zero trust, Gen. Morrison indicated. “Again, when you couple that with this notion of zero-trust principles, it increases operational effectiveness. It increases security. But it also will dramatically drive down costs.”
The two pilots will be only two elements in a coming year of dramatic progress, Gen. Morrison predicted. “We have established the foundations for how to do cloud. We’ve got the right contract mechanisms in place, and we also now have the establishment of C-Army, the Army’s instantiation of cloud. “The year that we are about to enter is a year of action and acceleration.”

Other examples of action and acceleration include the creation of a new theater signal brigade capable of performing command and control operations on the Department of Defense Information Network (DODIN) outside of the continental United States. “This year, from a force structure perspective, we will establish our first theater signal brigade that will now be able to do not only traditional network activities to support our garrisons and installations, but … be able to command and control, do those DODIN operation functions, operate, maintain, secure, defend and maneuver tactical formations,” he said, declaring it an “an absolute first for our Army” and adding that it will “be complete over in Europe by the end this summer coming up.”
He also predicted progress on cloud computing in the coming year. “You will see a much more rapid movement to the cloud over the next year. That foundation has now been set. We are putting the requisite capabilities into the hands of our operational formations so they can understand the applications. We are aligning the requisite combat power to assist in that migration. It’s just going to be much faster.”
Additionally, the Army expects great visibility into its networks. “You will see much more commonality in the capabilities that are going to be provided by Army Cyber [Command], so we can see the network end-to-end, to include into the tactical space. And then, more importantly, the ability to maneuver and defend it because we have thinking adversaries that are out there, and we need a command that can do that.”
The move toward unified network operations also will accelerate. “That acceleration into unified network operations will be a key part of what we’re doing. Again, we have the foundation established for us to do that. Now it is getting some of the disparate networks that we have inside our Army, which are now under the operational control of Army Cyber, onto these common capabilities because it’s only going to increase our defensive posture and our operational effectiveness, and quite frankly, the user experience.”
The general also touted the benefits of the Risk Management Framework 2.0, a cybersecurity assessment tool that cuts bureaucracy and saves time. The Risk Management Framework 2.0 drives down that bureaucracy, not so we can save money, but so we can put the appropriate resources into cybersecurity operations.”
Asked whether lessons learned from the war between Russia and Ukraine causes him to rethink any piece of the Army modernization plan or demonstrates the Army is on the right path, the general said the Army is on the right path but will continue to learn and adjust as needed. “We’re a learning organization. You see it through exercises. You see it through operations such as you just mentioned. We watch this stuff,” he said.
The service will continue “figuring out what ‘right’ looks like” and “what adjustments we need to make to any of our modernization programs, and quite frankly, to the force we have today,” he said.
“We’ve got to be adaptive. We’ve got to be thinking. Especially in the cyber domain. Our adversaries, they are adaptive. They are thinking,” he continued. “And the tactics, techniques and procedures they use today I guarantee you will not be the tactics, techniques and procedures they’re using even two months from now. As they adjust, we must learn, and we must adjust. We must do it faster than they can, hence everything we’ve talked about during this session.”




Comments