Mission Impossible: The Quest for Technology Acquisition and Advancement
Bridging the gap between today and tomorrow brings unwanted consequences. All change has disadvantages, and with a defense and security move toward a new era of technologies, novel challenges have arisen. It’s increasingly visible on Capitol Hill and beyond that agencies are concerned about the specific flaws in hardware and software and produce up-to-the-minute reports and directives. Nevertheless, there has been some neglect of unattractive parts of technology adoption—bandwidth, talent and red tape—creating a drag to capability acquisition.
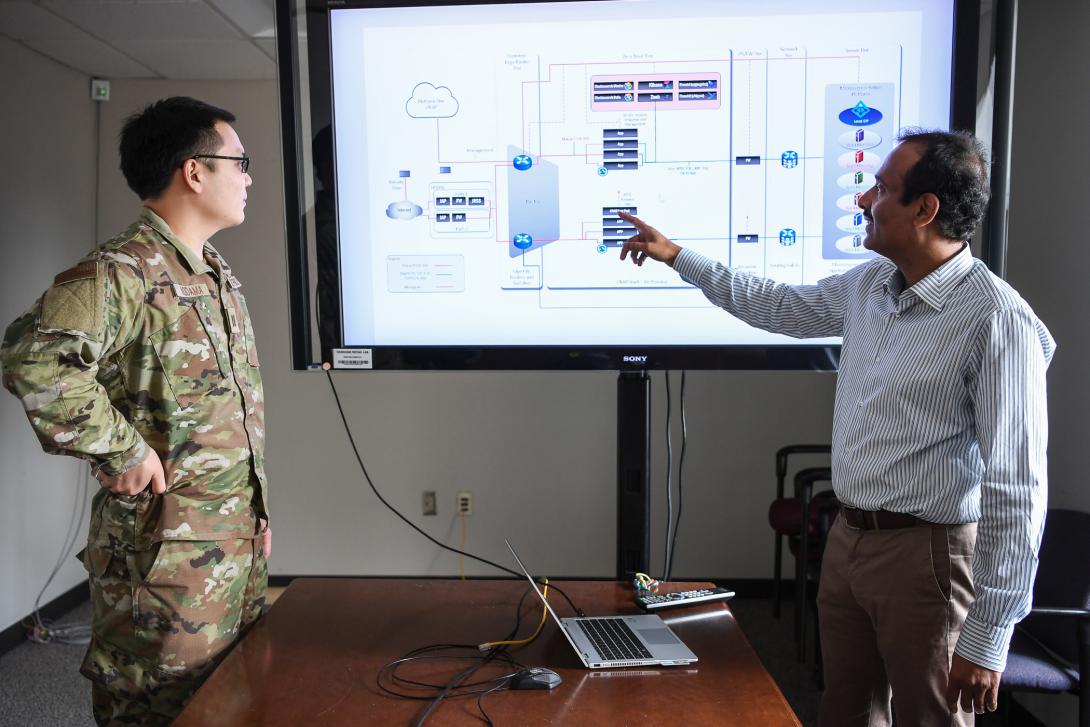
“What the Department of Defense understands is that they have unique applications and use cases and users, and the various ways that they’re going to interact with technology will be highly different than what is experienced in the commercial sector,” said Felipe Fernandez, director of systems engineering at Fortinet Federal.
New developments also offer advantages against adversaries. Nevertheless, basic design flaws could neutralize those potential benefits.
“When you move to [outside the continental United States], you’re working in other parts of the world—maybe forward deployed forces, things like that… you don’t have the bandwidth that you had when you designed the system or the application,” said Chris Hughes, co-founder and chief information security officer of Aquia and former Air Force cyber warrior.
Emerging technologies need increasing connectivity qualities, and some parts of the world cannot offer them. Thus, assumptions that went into design were adopted without thinking about the full set of constraints a user encounters.
Real-use scenarios need to be clear from the start of a project, and real-world constraints can be better factored in when design departs from the controlled conditions in the headquarters.
“That’s really where it comes down to having really solidified and clear requirements of where the application in the system’s going to operate in; so, you can design it with those constraints in mind,” Hughes said.
Humidity, dust or cloud coverage impact various aspects of technology operation in the field. Those conditions, or others, force developers to think outside the lab and walk a mile in someone else’s boots.
Hughes suggested the key to success is in taking a step back and before the first design assumption, “understanding who’s going to actually use this and where are they operating.”
A more persistent problem in technology adoption is the workforce shortage.
With unemployment at historic lows, hiring has been a struggle for all who seek talent, and the government must compete with businesses in this tight environment.
“Simply, the pay is not competitive often with industry,” Hughes commented in an interview.
For example, the massive adoption of cloud technologies in the government and the armed forces is in full swing. The benefits of using decentralized computing surpass the disadvantages, and that discussion is now outdated. Still, the whole job market is colliding with the realities of this demand in both the private and public sectors.
“Cloud professionals are currently the most sought-after tech talent and therefore have the ability to choose from an array of employment options that best fit their lifestyle,” said Laura Baldwin, president of O’Reilly, a company specializing in technology training.
Cloud professionals’ pay has increased by 4.3% in the year up to June 2022, according to figures compiled by O’Reilly. The 4.6% rise in federal salaries announced by President Biden in August would partially plug that gap, but job seekers are not only looking at the dollar sign.
“With these workers in such demand, we anticipate the great tech exodus to continue unless employers step up with competitive pay, substantial benefits, remote work flexibility and on-the-job learning and development,” Baldwin said in a statement.
And in this aspect, the potential failure could be compounded, as the benefits of working in an armed service, such as pride and camaraderie, are lost when civilian contractors are hired. And this is only part of the problem.
When contractors bid, the one offering the lowest price is the winner. “A lot of these [contractors] take what’s called LPTA, lowest price technically acceptable, and it essentially becomes a race to the bottom of who can have the lowest price for services,” Hughes said. “Then you get projects that don’t deliver anything. They’re behind schedule.”
Hughes explained that experienced leaders for these companies are priced out. Suppliers will not obtain the contracts they’re bidding for if they consider high-quality professionals. This means that oftentimes people whose skills are not quite up to par are responsible for projects that end up being “a bridge too far.”
Uniforms are not a panacea for the shortage either. The U.S. Coast Guard also has had problems staffing its cyber units despite its prestige and history.
A recent U.S. Government Accountability Office (GAO) report found that “the Coast Guard did not have a complete strategic process or plan for its cyberspace workforce that contained essential elements, such as a (1) strategic direction, (2) supply, demand, or gap analysis and (3) solution implementation, along with implementing activities to address all cyberspace competency and staffing needs.”
This resulted in a 9% shortage of staff in this field, as these positions were open but not filled, according to the GAO report.
The service has reacted and is already implementing recommendations.
“In an effort to address recruiting and retention challenges, the Coast Guard recently announced pay incentives for the civilian and active-duty cyber workforces,” said Capt. Adam Morrison, USCG, deputy, Coast Guard Cyber Command.
In reply to an email from SIGNAL Media, the authors of the report also added that civilian hires are the ones that seem especially hard to find.
“The difficult-to-fill positions we reference in the report are the civilian IT [information technology] management positions. The civilian IT Management Series covers positions that manage, supervise, lead, administer, develop, deliver, and support IT systems and services. It is the Coast Guard’s largest civilian cyberspace workforce position category, accounting for 58 percent of the civilian cyberspace authorized positions,” read the email by report authors Heather MacLeod, acting director, Homeland Security and Justice team; and David Hinchman, acting director, IT and Cybersecurity at GAO.

While the U.S. Coast Guard has taken a number of steps, including extensive training and a new enlisted rating and chief warrant officer specialty, the problem of finding talent is not limited to this service.
The same GAO report found that the staff shortage is widespread. “A resilient, well-trained, and dedicated cyberspace workforce is essential to protecting federal IT systems. Nevertheless, the Office of Management and Budget and our prior reports have pointed out that the federal government faces a persistent shortage of cybersecurity and IT professionals to implement and oversee information security protections to combat cyber threats,” the report stated.
While the extent of the problem is hidden under layers of secrecy by both government and private businesses, this report offers a glimpse into the issue.
“In recent years, its networks and information have been exploited and maritime critical infrastructure have experienced cyberattacks. For example, according to the Coast Guard, over 500 cyber attacks occurred within the marine transportation system in 2020. It estimated that the cost of a data breach in general was about $3.9 million, on average,” read the report. Therefore, this math suggests that in 2020, attacks on the marine transportation system would have cost $2 billion.
Other parts of the government could tell similar stories.
Personnel isn’t the only area where new technology deployment runs behind events.
“Part of the challenge for the federal government right now, is that they use a couple different frameworks or governance structures to adopt cloud. First is FedRAMP at the federal civilian level,” Hughes explained.
The Federal Risk and Authorization Management Program, FedRAMP, is the procedure used to approach security authorizations for Cloud Service Offerings, according to its website.
In the case of defense, obtaining the first authorization is only the beginning. After FedRAMP comes the Security Requirements Guide for use among Department of Defense (DoD) agencies.
“So, you could have a cloud service come out and say from Amazon, for example, and it could be 18 to 24 months before that service gets in the hands of Department of Defense; so, you’re talking, several years of lag time and when it comes to getting access to innovative cloud services, just due to these governance and compliance frameworks that they have to deal with,” Hughes said.
Out of thousands of available cloud services, for example, only 281 are currently approved by FedRAMP. From that pool, the DoD has to pull the ones it will use from private suppliers for subsequent approval.
In many cases, by the end of the process, the innovation is no longer new or the startup that came with it no longer exists. This means that a gap that could have been plugged by innovation in development, deployment or even quality assurance will cease to be available.
“Many senior leaders have articulated [adoption of cloud services] as critical for national security, citizen services and competing against foreign adversaries, but you’re really limited in how accessible those cloud services are,” Hughes said.

Comments