Search Results for "" The Cyber Edge ""
GE Appoints Mohammed President GE Energy Connections’ Power Conversion
GE appointed Azeez Mohammed president and CEO of GE Energy Connections’ Power Conversion business, based in Paris.
Delta Risk Names Hendricks Vice President
Delta Risk LLC, San Antonio, named Chris Hendricks vice president of security operations services.
Cylance Hires McClurg as Vice President
Cylance, Irvine, California, hired John McClurg as vice president in the Office of Security and Trust.
Huntington Ingalls Industries Appoints Leonard Corporate Director
Huntington Ingalls Industries, Newport News, Virginia, appointed Capt. Joseph J.
Host.net Appoints Russo Chief Technology Officer
Host.net, Boca Raton, Florida, appointed Nick Russo chief technology officer.
Worth Appointed Vice President of Business Development for Seidor
Eric Worth has been appointed vice president of business development and head of the Northeast region for Seidor, Housto
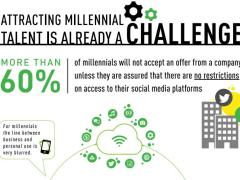
Millennial Cyber Behaviors Threaten Federal IT Systems
Millennials could just pose as grave a cybersecurity risk to enterprise networks as cyber criminals, according to one recent study. With more of them entering the federal workplace, they bring along technology preferences and bad behavior that threaten security of federal IT systems, according to cybersecurity developer Forcepoint.
DNI James Clapper Talks Pre-election Uncertainty and Global Instability at EPIC Event
The next 17 days leading up to the presidential election pose a rather vulnerable time for the United States—more so than usual during a transition of power, says Director of National Intelligence James Clapper. “This year, for lots of reasons, people are nervous, particularly for an election cycle that has been sportier than normal,” Clapper shared during at presentation Thursday at AFCEA’s Emerging Professionals in Intelligence Committee (EPIC) speaker series.

The Benefits of Automation for Sensitive Content Management
The increased focus on the sharing of information—whether among U.S. agencies or with international allies—has resulted in an expanded reliance on content management systems. These platforms enable collaboration on an enterprise-wide scale, letting groups across the Defense Department and NATO effectively share mission-critical information and documentation.

DHS Has More Than 120 New Cyber Hires
Department of Homeland Security Secretary Jeh C. Johnson gave a report on the department’s progress in cyber hiring, announcing more than 120 new employees.