Where’s the Map? Dora, DCO and the Future of Cyberspace Defense
Where’s the Map?
If you’ve ever watched Dora the Explorer, you know the song: “Where’s the Map?” For Dora, the Map is not a background prop. The Map has “main character” energy. In fact, Dora cannot even begin most adventures without it.
Yet in the Department of War’s (DOW’s) defensive cyberspace operations, we have been trying to defend without a map of our own (or at the very least a holistic and detailed one). Despite decades of doctrinal recognition that cyberspace is a warfighting domain, our defensive cyberspace operations (DCO) teams often fight blind. We have inventories of devices and ad hoc diagrams, but no comprehensive picture of the terrain we are tasked to defend. We don’t connect the terrain we defend to the reason we defend it—the mission!
This absence is striking when compared to other domains. Land forces rely on topographic maps. Naval forces use navigation charts and bathymetric data. Air operations are structured around airspace control measures and tasking orders. Space operators build situational awareness from orbital trajectories and spatial mappings. But cyberspace? Our “maps” are fragmented at best.
A recent Government Accountability Office report highlights DOW’s effort to consolidate cyberspace enterprise functions, over 400 organizations and roughly 60,000 personnel engaged in overlapping missions. This call for consolidation and alignment is a rare opportunity. As the department streamlines structures and reduces duplication, we should seize the moment to equip our cyber defenders with the one tool every other domain considers indispensable: a map.
What a Blue Cyberspace Map Would Look Like
Joint doctrine already provides a starting point. Joint Publication (JP) 3-12 (Cyberspace Operations) and Air Force Doctrine Publication (AFDP) 3-12 (Cyberspace Operations) describe cyberspace in three layers: physical, logical and persona. But in practice, these remain abstract.
A real map must capture dependencies—the things our missions rely on every day. That may mean expanding doctrine into a map with more layers, for example:
1. Physical Layer: The foundational layer of cyberspace terrain consisting of electricity, fiber, Wi-Fi spectrum, devices, sensor (IoT) assets, etc. This layer defines what physically exists and provides the bedrock for all higher-level functions.
2. Logical Layer: The virtual and software-defined elements that organize how systems interact. This includes operating systems, virtual machines, routing protocols, cloud environments, containers and VPN tunnels. It answers the question: How does a system operate as a system-of-systems?
3. Persona Layer: The human dimension of cyberspace encompassing users, administrators, credential holders and adversaries operating within or against blue networks. This layer reflects who is acting within a system.
4. Functional Layer: The mission-essential functions, workflows and command-and-control processes that lower layers depend upon. This is a further abstraction and more robust understanding of the first three layers. This layer ties cyber terrain directly to operational outcomes, answering the question: What mission or process does our terrain support?
5. Dependency Layer: The external infrastructure and services that blue missions rely on but often fall outside of the DOW to control. This includes telecommunications providers, internet service providers (ISPs), cloud service operators, contractors and supply-chain information technology (IT) and mission-dependent operational technology systems. This layer captures what outside systems sustain or constrain our missions.
In land, sea, air and space domains, forces overlay multiple maps to build terrain understanding. In cyberspace, it’s time that we do the same.
The addition of “functional” and “dependency” layers on a map isn’t anything new, and this isn’t a departure from how the Joint Force already uses maps in other domains. Land maps highlight bridges, roads and other key terrain; sea charts overlay shipping lanes and ports; air maps show corridors, tanker tracks and restricted zones; space diagrams mark orbital slots and ground stations. These are all functional or dependency overlays. These are all features that tie terrain directly to missions and reveal the external enablers that sustain operations.
Cyberspace requires the same treatment. The Functional Layer connects cyber terrain to mission-essential functions and workflows, answering the what the system supports question. The Dependency Layer surfaces external infrastructures like ISPs, telcos, sensors and contractors (the equivalent of lines of communications, straits, tanker tracks or ground stations), answering what does our mission rely on?
Unlike physical domains, cyberspace dependencies are often inconspicuous, intangible, volatile and deeply interconnected. Making them explicit as map layers ensures cyberspace forces gain the same mission-focused clarity their peers defending other domains have always relied on. Efforts have been made to map these dependencies, such as Functional Mission Analysis Cyber and Operations systems design methodologies. These efforts must extend further and provide critical data faster.
Why It Matters
Defensive cyberspace operations are mission assurance at digital speed. Without a holistic blue map, defenders and automated systems will spend time reacting and processing alert significance rather than understanding the impact of threats and vulnerabilities within the operational environment.
Consider a squadron preparing for flight operations. If the runway were under repair, the unit would immediately understand the risk because maps, schedules and dependencies are documented and visible. In cyberspace, however, if a base’s fiber link to its ISP is severed or a contractor’s IoT system is compromised, the downstream mission impact is often unclear.
This is more than an efficiency issue; it is a strategic vulnerability. As JP 5-0 (Joint Planning) notes, joint planning must be informed by a full understanding of the environment. Without explicitly mapping and understanding our functional and dependency cyberspace layers, planners and operators lack visibility into what missions terrain supports and what external infrastructures sustain them. Standardizing these layers as part of our cyberspace paradigm and paying attention to them as networks are built, operated, sustained and extended ensures cyberspace defense priorities are correctly aligned. These additions also enable our cyberspace defensive forces to anticipate mission impacts with the same clarity afforded to other domains.
Technology Can Help
The good news is that the tools now exist. Advances in generative artificial intelligence (AI) and machine learning (ML) can automate many of the functional and dependency mapping challenges, especially as solutions are approved and deployed at the edge and appropriate classifications. Algorithms can:
• Build logical-to-physical dependency graphs.
• Identify external infrastructure links (ISPs, telcos, cloud providers, etc.) that sustain missions.
• Map cyber terrain directly to mission-essential functions, highlighting where a disruption in one layer cascades into another.
• Continuously update these maps as networks, providers and workflows evolve.
This isn’t a replacement for human judgment; it’s an augmentation. Just as satellite imagery enabled precision mapping in land operations, AI-enabled discovery can finally give us a holistic blue terrain picture in cyberspace. By making functional and dependency layers explicit, these technologies can help commanders at all levels of battle see not only where cyber terrain exists, but also what it enables and what it relies upon.
Doctrinal Alignment
This proposal does not require inventing a new doctrine; it requires extending existing doctrine to cyberspace with the same seriousness applied to other domains.
• JP 2-01 on Intelligence Preparation of the Operational Environment emphasizes terrain analysis as foundational to planning.
• JP 3-0 defines maneuver and movement as inseparable from terrain understanding.
• JP 3-12 already acknowledges cyberspace layers but leaves them abstract.
By institutionalizing blue terrain mapping within Joint Intelligence Preparation of the Operational Environment and aligning it with AFDP 3-12, the Joint Force can normalize maps as part of cyberspace operations.
Recommendations
1. Institutionalize Blue Mapping. Update doctrine (JP 2-01, AFDP 3-12) to require blue mapping of all five cyberspace layers with particular emphasis on functional and dependency overlays. These updates should be seen as an operational necessity to ensure terrain maps are mission-linked, not just machine-linked.
2. Leverage Consolidation Momentum. As the DOW consolidates more than 400 organizations and 60,000 personnel in the cyberspace enterprise, standardize terrain data models, data feeds and formats that explicitly include functional and dependency layers. These outputs should be tied to mission-essential functions (as outlined in the Unified Campaign Plan) so that consolidation results in actionable mission assurance products, not just reduced overlap.
3. Operationalize Blue Terrain Intelligence. Establish a Joint Concept for Cyberspace Terrain Awareness that codifies the blue map as doctrine, aligns to JP 5-0 and incorporates AI/ML to improve environmental understanding. Blue cyberspace terrain products should then be integrated into the joint planning battle rhythm alongside traditional intelligence, weather and logistics overlays.
The Dora Lesson
Dora the Explorer never set out on an adventure without the Map. The rambunctious explorer knew that it was the guide that showed not only where things were, but how to get where she wanted to go and what obstacles to expect along the way. In the same thought, cyberspace defenders cannot afford to operate without a map that captures the physical, logical, persona, functional and dependency layers of their terrain. This becomes even more important as adversaries mature their capabilities and take on algorithms that will push our defensive needs to machine-speed reaction time.
Other domains have long relied on such overlays to link terrain to mission and expose critical dependencies. Now, as the DOW consolidates its cyber enterprise, we have an opportunity to make the cyberspace map a main character in DCO. Without it, our forces risk wandering blindly and without priority; with it, they can defend with clarity, anticipate impacts and assure the missions that depend upon cyberspace every day.
Maj. Nathaniel “Nate” D. Hicks is a cyberspace operations analyst and executive officer for the Program Analysis and Evaluation directorate within the Office of the Secretary of the Air Force. Hicks’ career includes assignments as a blue team technical director, an instructor in information operations and a fellow in the Air Force’s Education with Industry program at Google. He holds a Master of Science in information technology management from Trident University International and a data analytics certificate from the Air Force Institute of Technology.
DISCLAIMER: The views expressed are those of the authors and do not reflect the official guidance or position of the United States Government, the Department of Defense the United States Air Force or the United States Space Force.
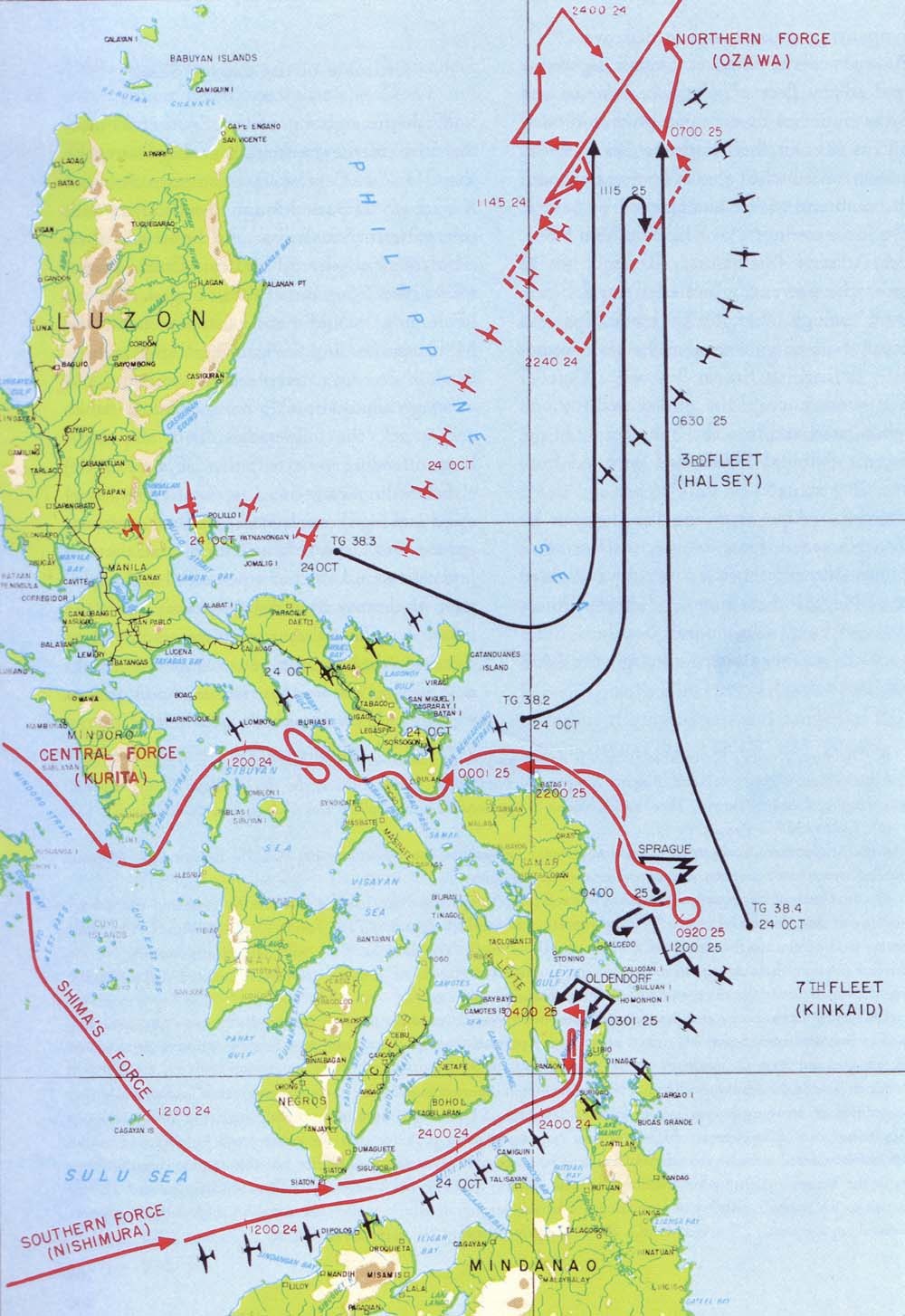
Map of the Battle of Leyte Gulf (1944),
the largest naval battle in history, showing the Allied naval forces’ maneuvers. Naval planners relied extensively on charts to coordinate multifleet operations.
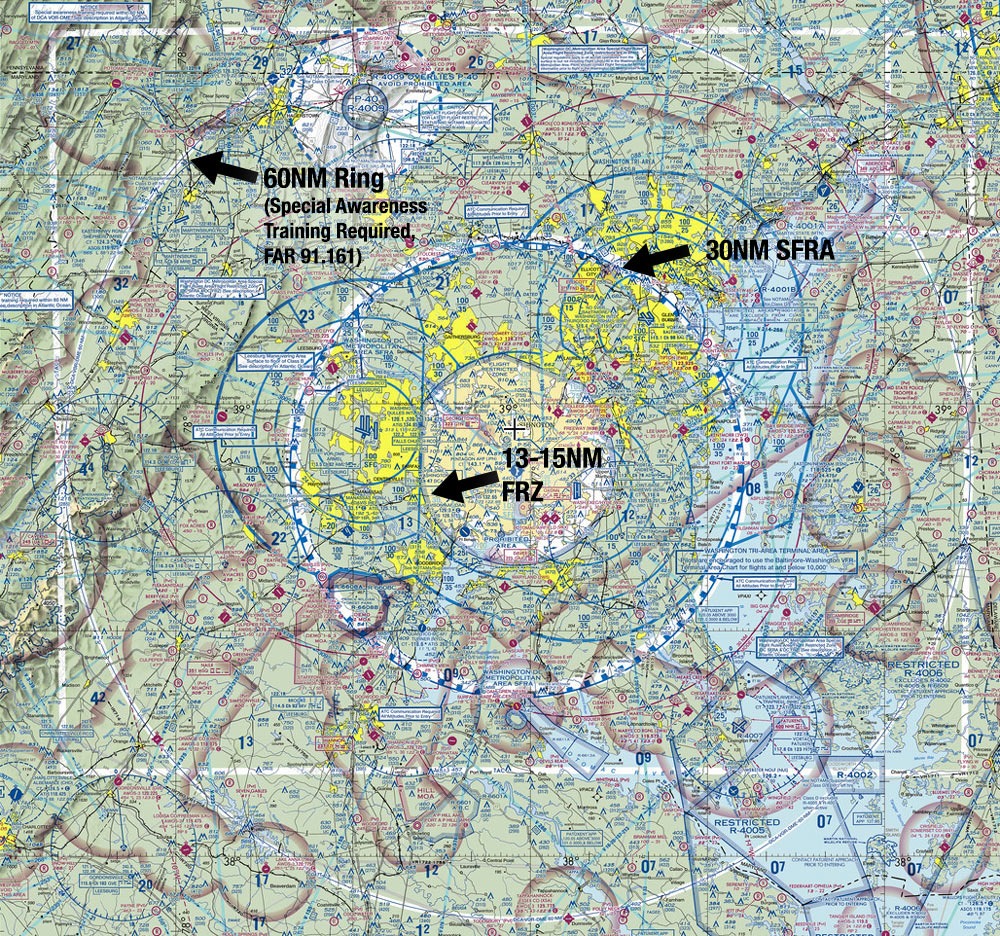
Airspace diagram showing the Special Flight Rules Area (SFRA) and the Flight-Restricted Zone (FRZ) around Washington, D.C., highlighting the importance of controlled airspace for national security. This map represents critical air corridors used by civilian and military aircraft, with strict procedures for accessing these zones, much like how cyberspace traffic must be carefully managed and controlled.
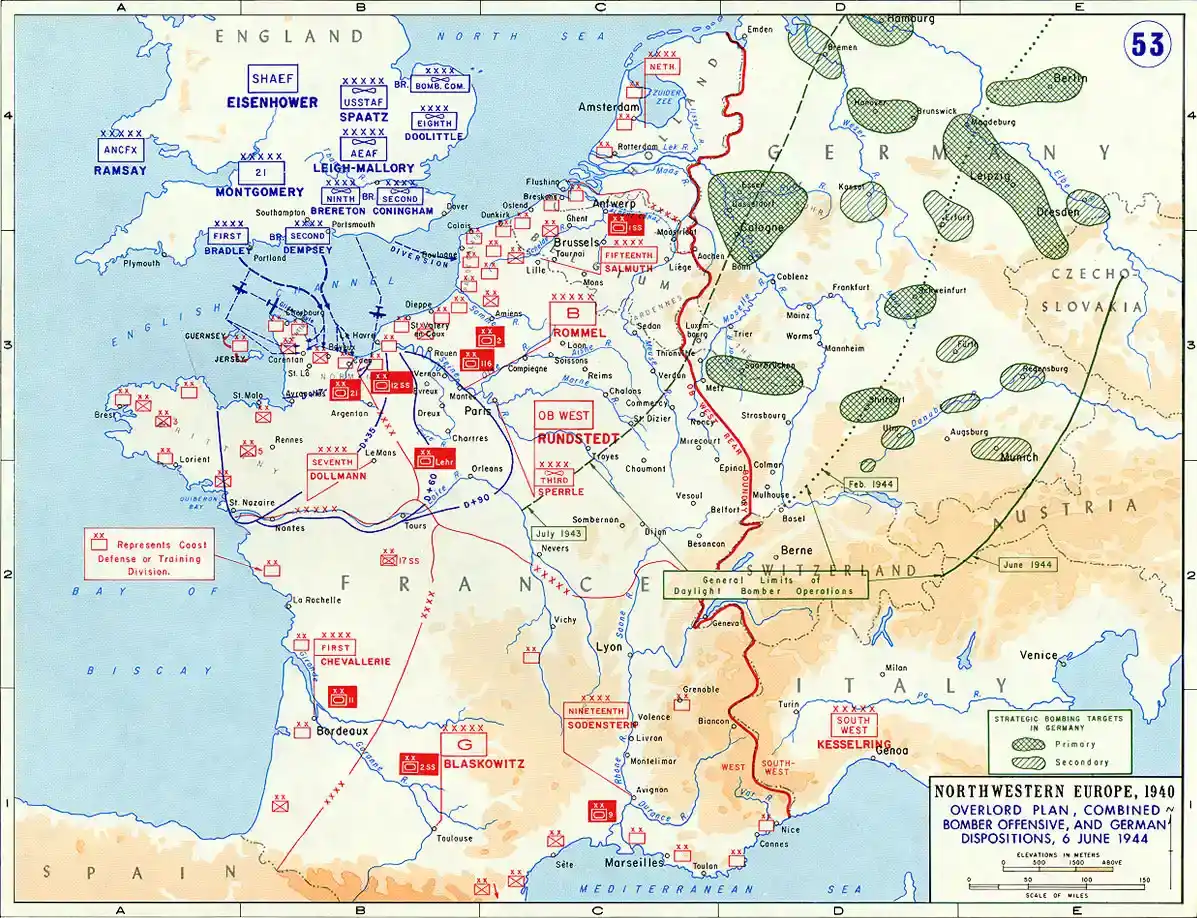
Map of Operation Overlord, 1944. Allied forces’ strategic planning for the invasion of Nazi-occupied France during World War II shows troop dispositions, air and ground routes, and key terrain. This operational map illustrates how detailed terrain overlays are crucial for coordinating large-scale military campaigns, similar to how cyberspace defenders need a blue map to guide mission assurance.
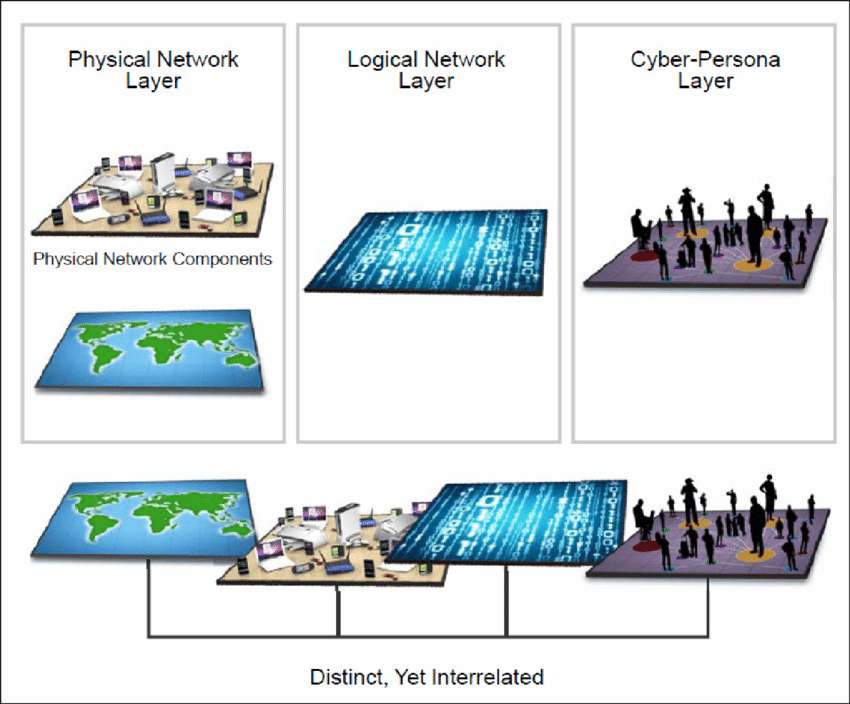
The three interrelated layers of cyberspace (from AFDP 3-12), showing the physical, logical and cyber-persona layers. These layers define cyberspace terrain, connecting physical network components, logical networks and cyber actor, essential for understanding the terrain our cyberspace defenses must protect.

Comments